Mastering OLAP Cube Reporting: Solving Grand Total Calculations in Snowflake Warehouse and AAS Cube Projects
March 27, 2024 5:28 pm
Welcome to the first installment of our promised series of articles detailing the challenges we encountered and conquered during our work on the “Snowflake Warehouse and AAS Cube” project.
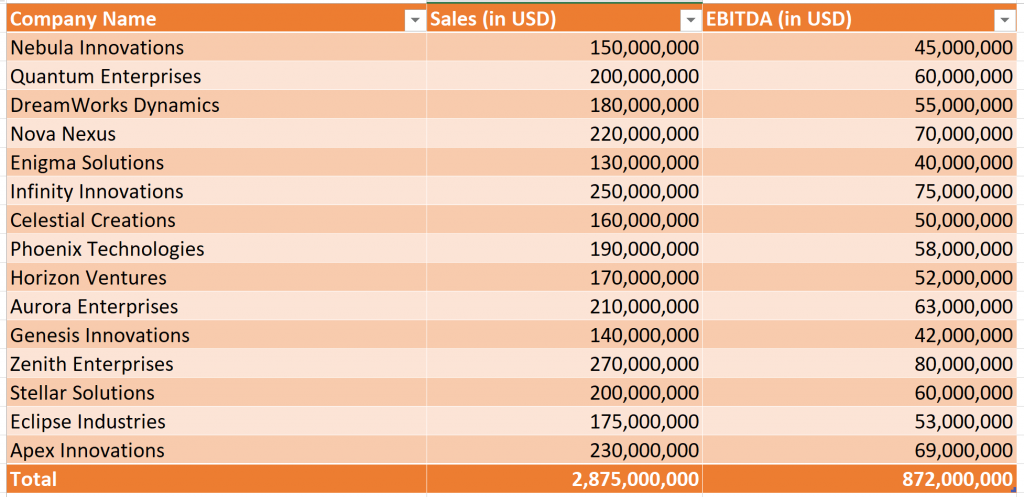
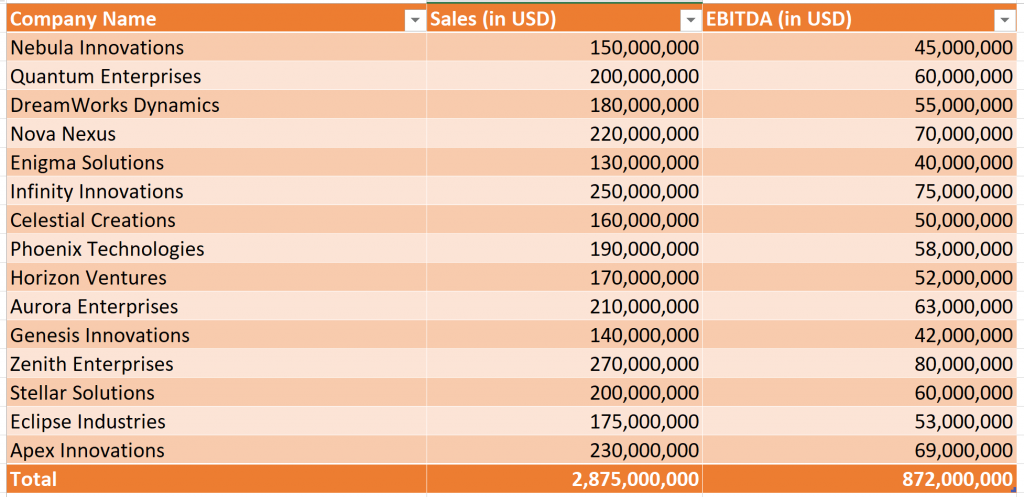
Today, we’re excited to share how we tackled a particularly thorny issue while developing an AAS Cube project for one of our valued clients. Our task involved creating measures to extract financial data such as Sales and EBITDA. Given that reports are generated in specific currencies (e.g., USD), we needed to incorporate currency (FX) conversions within these measures. The parameters for these calculations varied depending on the particular company, with each company having its base currency code. More
Automatically set unique permissions in SharePoint with Microsoft Flow
April 24, 2019 8:15 am
We have a customer who is using SharePoint Online and they recently asked us to find a solution for the following situation in the Documents library.
There are a couple of root-level folders which are shared with specific user groups using a special permission level which doesn’t allow the users to delete those parent folders. However, the customer needs to allow the users to create new sub-folders and also delete them. The problem is that the sub-folders automatically inherit the permission settings of their parent folder which doesn’t allow the delete operation. So, they need to automatically break the inheritance and set appropriate permissions for the new sub-folders.
We found that Microsoft Flow is a great tool which helped us to resolve this problem by automating the process of breaking the default permissions inheritance and setting the desired permissions in SharePoint.
In this particular request we need to programmatically break inheritance of permissions for a given file/folder. Also, we need to assign unique permissions for that file/folder. These operations could be performed programmatically by calling the SharePoint REST API. This is a secured API and all API calls should be authenticated and authorized. This authentication is based on access tokens.
We ran into some peculiarities while implementing the solution and that is why we decided to share our experience here.
More
Mobile App with Corporate Authentication (Ionic + ASP.NET Web API + OAuth 2.0 tokens + Okta)
December 9, 2015 4:06 pm
Recently we had to build a mobile application and one of the requirements was to implement a corporate authentication for managing the user accounts. We think the approach that we used could be interesting and helpful in similar scenarios that is why we would like the share our experience.
The app that we built is simple and allows pulling and displaying some corporate information for authenticated users. Following are some details about the technologies that we used to build the app:
- Ionic – We used the Ionic framework to build the mobile app itself. Ionic is a great framework for building hybrid mobile apps. It is based on AngularJS and provides handful components and tools. The apps build with Ionic are easily distributed to iOS and Android devices.
- ASP.NET Web API – We used the ASP.NET Web API 2.2 to build the server part. It pulls the data from the database and sends it to the mobile app in JSON format by implementing a RESTFul API. It also handles the authentication part by implementing part of the OAuth 2.0 protocol.
- Okta – Okta is a third-party authentication provider and our client had already been using it for managing their Active Directory accounts.
In short, the mobile app sends the credentials to the API server which is responsible to validate them by communicating with Okta. Once the credentials are validated then it generates a token which is stored on the mobile device and used for further communication between the mobile app and the API server.
More
TinyMCE in ASP.NET UpdatePanel
December 20, 2014 12:03 pm
TinyMCE is a great HTML editor and it is pretty easy to install and configure the editor on a web page. You should just call the init() function while loading the web page at the client’s browser and the target text-area will be transformed into a nice looking HTML editor.
However, we run into some troubles when we tried to use the TinyMCE editor on an ASP.NET page containing server inputs that are handled by the Microsoft’s UpdatePanel control.
More
Online Technical Documentation based on WordPress
December 11, 2014 4:32 pm
Recently, we were asked to implement an online technical documentation solution by one of clients. We had to move the existing offline documents (mainly MS Word and PDF files) to an online accessible format that would also allow the users to modify the documents by themselves. We thought about the following options for implementing this:
- Implement a custom web based ASP.NET solution, starting from scratch
- Use Wiki engine
- Use CMS (e.g. WordPress)
We did not choose the custom implementation because it was the most time consuming option. We also did not choose the Wiki software because we found it a bit outdated and too restrictive and finally we focused on the CMS solution.
More
WIF SSO and Forms Authentication in ASP.NET
December 8, 2014 4:43 pm
One of the projects on which we are working is a long-lived ASP.NET Web Forms system that is customized for a specific client. It is hosted by another company on a server which is external to the client’s environment and it does not have an access to the client’s internal network. The system is built by using the Form Authentication mechanism to authenticate and authorize the users. The list of users and their hashed passwords is stored into the database and the login functionality works in a classic manner – the credentials provided by the user on the login page are validated against the list of users in the database. If the provided credentials are valid then a new Forms Authentication session is established by calling the standard method FormsAuthentication.SetAuthCookie().
Recently, we had to extend that authentication mechanism by adding a single sign-on (SSO) capability which allows the client to integrate the ASP.NET web application with their internal Active Directory (AD) infrastructure. The requirement was to allow some internal employees to access the ASP.NET web application through SSO, but also keep the exiting database login functionality for the rest of the users who are external and they do not have internal AD accounts.
The ASP.NET web application is hosted on an external server and it does not have a direct access to the secured AD infrastructure. After doing some research, we found that in order to connect the external ASP.NET web application to the internal AD environment we can use a middle service called Security Token Service (STS).
More